The Dark Web, a mysterious place and playground for criminals? Is it safe to go there and am I doing something illegal? Can I really find study material there you might think?
First of all, getting into the Dark Web is not difficult, illegal or dangerous if you know what to do. However, there are risks involved that can be avoided by following the steps below:
- Know what the Dark Web is and what not
- Make sure you have a secure connection to the Internet
- Prepare your computer and install a special browser
- Accessing the Dark Web
- Getting a safe anonymous email address
- Finding study material
So let me take you on a tour to “the dark side” and you will see it is not as scary or difficult as you might think.
What is the Dark Web?
The Dark Web is a part of the Deep Web which you also might have heard before and possibly even confused. So simply put the Deep Web are all websites that traditional search engines like Google cannot find. But how can that be? To understand that you need to know how Google searches websites.
When you type in a search term a search engine does not “go out” and look for relevant information on the Internet. All those relationships between your search and possible results are already in Googles Database. They send out robots all the time to crawl the Internet and find new content, following links and indexing pages that have been submitted to Google. And now j
So how does the Dark Web fit into the picture? The content of the Dark Web can also not be found by traditional searches because it contains sites on an encrypted network. Most of the websites there use the Tor encryption protocol to hide their identity. To see those websites you need to use the Tor Browser which is freely available on the Internet. Though this might sound scary at first it is actually a good thing. Nowadays when you surf the net you are leaving huge footprints that are picked up by all kinds of services to create a profile of you and bombard you with spam and advertisements. It starts with your internet provider tracking what you watch when and where – continues with Google or other search engines and definitely does not stop with social media that collects all the data they can get their hands on. So using Tor (even for your normal Internet use) is something to consider if you want to keep a bit of privacy. While for surfing in the Surface Web encryption is highly recommended but optional it is (in my view) mandatory to visit “the dark side”. Let’s take a look at this.
How to secure your internet connection
Apart from using Tor, there is an additional step (which actually has nothing to do with the Dark Web) that I highly recommend and use myself ever since I have lived in China. Use a VPN connection. If there is 1 thing you should do when going online it’s this. VPN stands for Virtual Private Network and accessing the Internet through a VPN not only hides your identity but also encrypts your traffic. This means that not even your internet provider can see where you are going and what you are doing. This is not about hiding illegal activity, it is about protecting your data. Unfortunately, these services are not free. There are free versions available but when it comes to security it is better to trust your data to a market-leading proven provider rather than some no-name company. No worries, it is not that expensive and with 3-5$ per month, you can have the perfect security solution. If you are not willing to spend that kind of money I recommend not to go to the Dark Web but to a library to find study material.
If you are still with me let me show you what to look for choosing a VPN provider and how to use it. Here are some quality criteria:
- Speed
- No logging policy
- Killswitch
Speed: Why does speed matter? To understand that let’s take a look at how these services work. Without going into technical details when you enter a website into your browser the request will not go directly to the destination but rather to a computer under the control of your VPN provider, a so-called proxy. This server can be anywhere in the world (which you can usually choose). Now the request is being forwarded to the real destination, then the result is taken and send back to you (all encrypted of course). This means that wherever you go the destination computer never knows you have visited, it just sees the proxy. Techies will probably cry now because this is quite simplified but this is not a technical post. Anyway, you can imagine that relaying all that information through another computer takes additional time, so if you don’t want your surfing experience to be sent back to the 90s a speedy provider is something to look for.
No logging policy: Some providers safe where you go and when and others don’t. This means even the destination server does not know it was you the VPN service provider still does. So the one I am using and recommending (NordVPN) deletes all tour traffic and does not keep any records of your activity.
Killswitch: Another necessary feature when using a VPN is that it has a killswitch. When you connect to your VPN provider you need to install and go through a little software tool that makes the connection for you and ensures everything is encrypted. You can get this tool from the website of your provider and it should be available for all platforms including mobile. A capable user can even install it directly on the Internet router so everyone and everything that connects to your home network is safe. But what happens if the connection drops? In this case you can configure a killswitch to do one of 2 things:
- Stop all internet traffic until the secure connection is back up
- Kill previously specified programs on your computer
Both of these options are very useful depending on what you do to prevent that you are accidentally connecting through an insecure channel. So, let’s prepare your computer and set this up.
So, using a VPN and Tor is already safe enough. But there is something else you can do if you are still feeling uncomfortable. This 3rd layer of security is called VM (Virtual machine). This is basically a simulated computer on your computer. The purpose of this is to protect your “real” notebook. If you do download something dangerous or your simulated system looks or behaves strangely you just delete the whole computer. This is like trashing your laptop when you catch a virus. A VM lets you separate your Dark Web excursion completely from your “normal” surfing. This way you can completely erase all traces of ever being on the Dark Web by just deleting the Virtual Machine. There are 2 ways to do this:
The complex method – Create a Virtual Machine by yourself – You basically need to install an operating system of your choice from scratch with the help of VM tools depending on the OS of your “real” computer. To explain this would be too much for this post, there are detailed tutorials on how to do this on the internet if you are interested.
The easy way – Download a free ready to use virtual machine – Other people have already done the work so you can just go ahead and use one of those “virtual boxes” and get started. Let’s dive into this.
Preparing your Computer
Preparing the virtual machine
If you decided that VPN and Tor are good enough (and it is) just skip to the next chapter where we set up the VPN.
To get a VM up and running you need to download 2 things. The “container” software. This program holds your virtual machine and manages the isolation between your real computer and the virtual one. It can provide you with every possible operating system out there, just think of it like a coffee machine where you can insert different types of capsules for different flavors. So go to VirtualBox.org and download it for your platform and install it. Before we set it up we need another thing, the guest system.
Since we want to keep this simple (and free) we cannot use Windows as an operating system for our Virtual machine – except you have an unused old Windows installation DVD which you are not using anymore. So what we need to use is – Linux. Don’t get scared, we just use it for browsing on the Internet and if you have never seen a Linux System you might even like it. No worries I will take you through it and it is easier than you expect.
Creating an Ubuntu Virtual Machine
Linux has several different editions created by different people or companies. In our case, we will use a Version called Ubuntu. Go to osboxes.org to the Ubuntu section by clicking here. You will see a list of versions, download the latest one by clicking the download button under the VirtualBoxTab

Now, unzip the package you just downloaded (in the download folder is fine, we just need it once.
No start the VirtualBox app you downloaded previously. You should see a window like this and follow the steps below:

- Press the blue ribbon-shaped new button, a popup opens like in the picture
- Type in a name for your virtual machine, for type select Linux and for version Ubuntu 64 Bit like shown in the picture
- Adjust the memory to a higher value and make sure it stays in the green area (preferably 4096 if that is still in the green area on your computer). The amount you can pick here depends on your internal memory. Don’t think about it too much, if the VM runs too slow later you can still adjust this value.
- Select “Use existing Virtual Hard Disk file
- Press the tiny yellow folder and navigate to the folder where you have unpacked the Ubuntu download. The folder is usually called 64Bit. Inside look for a file with the ending
vdi (Should have a red cube icon) and select it. - Hit the create button and wait until it is finished.
Now you should see the following entry on the left side:
That’s it. Wasn’t too hard, was it? Now select the entry you just created and press the green start arrow to fire up your computer on your computer. This can take a while and when it is finished you should see your new Linux computer running in a window like this:
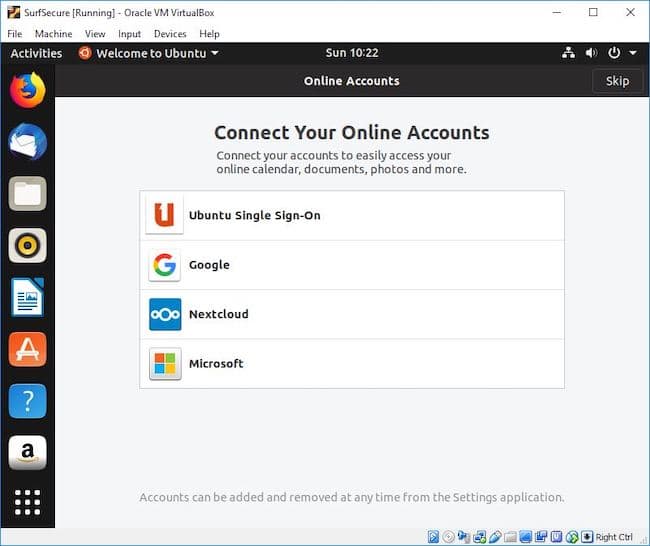
Ubuntu has a normal user management like all other operating systems so you need to login with a username and password which is osboxes.org. During the first start Ubuntu asks you for some initial setup steps, hit the skip button in the upper right corner.
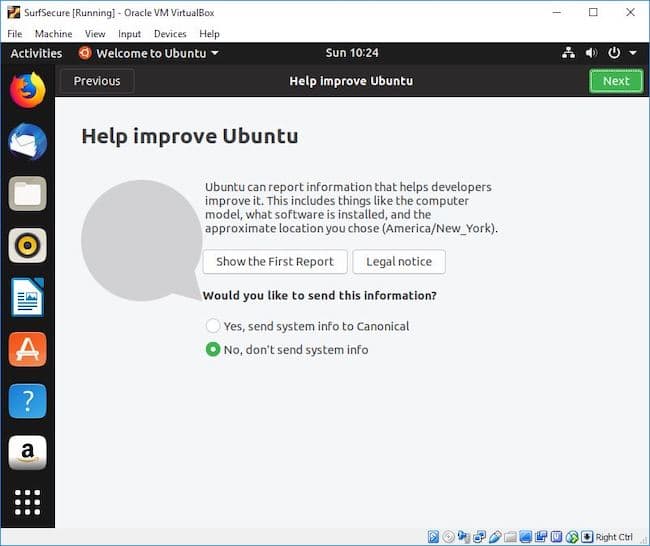
Here switch to No, don’t send system information and press next, after this just press the Done button on the last screen. I recommend you make yourself familiar with Ubuntu a bit, you will realize that it is probably similar to what you know already and if it is your first time with a Linux system you might be surprised how “easy” it is to use.
Now our VM is ready. But before we continue to download and install Tor we will install and configure our VPN on the “real” computer first.
Setting up your VPN
Getting a secure connection is fairly straightforward. The first thing you need to do is set up an account at NordVPN if you haven’t done that already. They always have promotions of up to 2.99$/month which is a really good deal for privacy. I am very happy with them for years and my VPN is switched on all the time (except when I am playing a game). Now download the software for your operating system and install it. After you start the software it is a 1 click security:
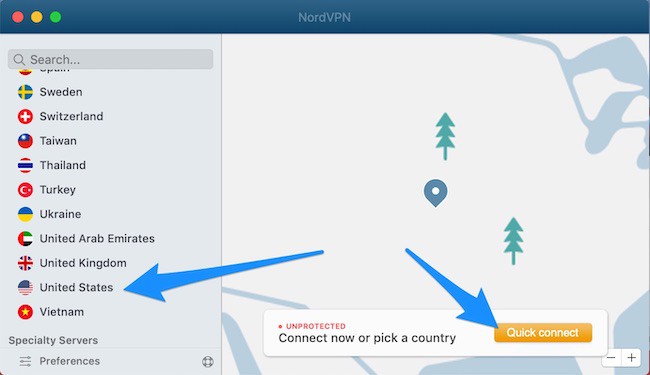
NordVPN detects where you are and automatically connects you to a Proxy Server in your country if you just hit the Quick connect button. You can, of course, pick a country by yourself on the left (which is usually a slower connection) but can be useful (e.g. if certain services are bound to the country you registered them in like Netflix you can trick them into thinking you are coming from somewhere else).
Activating the Killswitch
Now, before we proceed to install the browser let’s configure the kill switch:
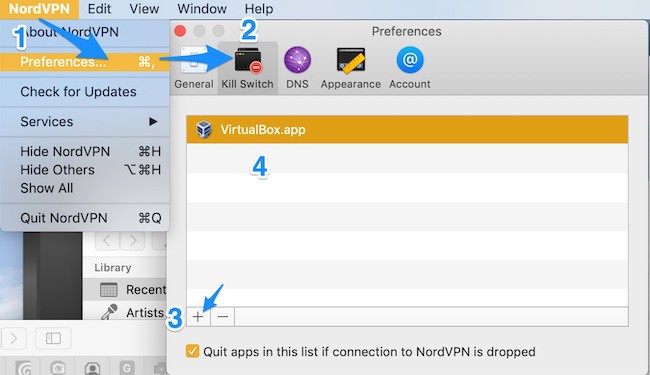
- Go to your main menu and click on preferences
- Switch to the Kill Switch Tab
- Press the Add (+) button
- Find your VirtualBox.app (or
exe on a windows computer)
What this does is if your secure connection drops for any reason your virtual machine will be terminated immediately so that no unwanted traffic goes over your Internet connection)
If you skipped the part to create a VM, of course, you need to add the Tor browser here after we went through the installation in the next step.
Installing the Tor Browser
First of all, make sure your VPN is enabled. Again, if you have skipped the VM just go to www.torproject.org and download the Tor Browser for your operating system and install it like any other program. For those of you who picked the VM here are the details:
Go to the Tor page and locate download page, then download the Linux 64-Bit version (Purple button)

Once the download is finished:
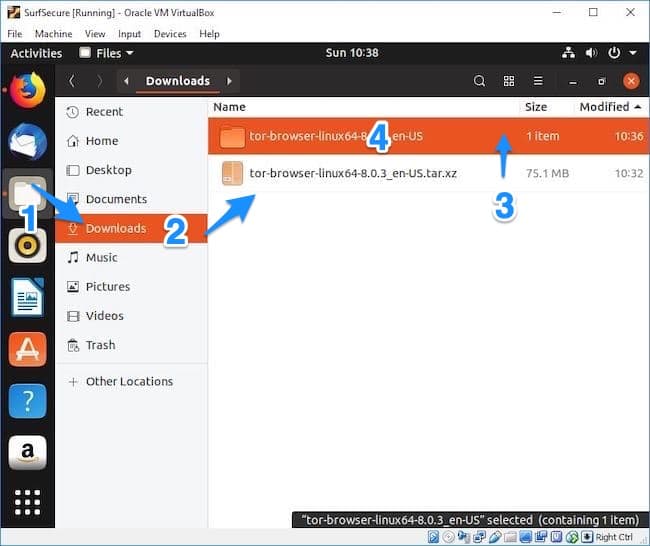
- Press the grey icon folder on the left
- Go to the Download folder
- Double click the file with the tar.xz ending – it will unpack automatically
- Go into the newly created tor browser folder
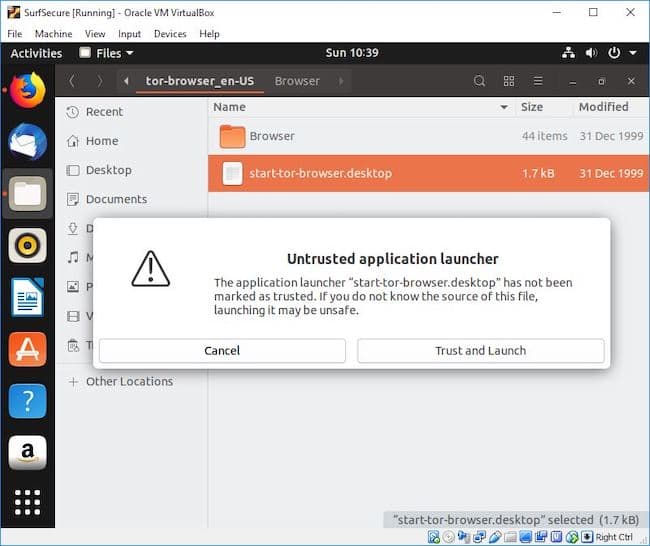
Once entered the tor folder double click the start-tor-browser.desktop and confirm the popup by pressing on “Trust and Launch”.
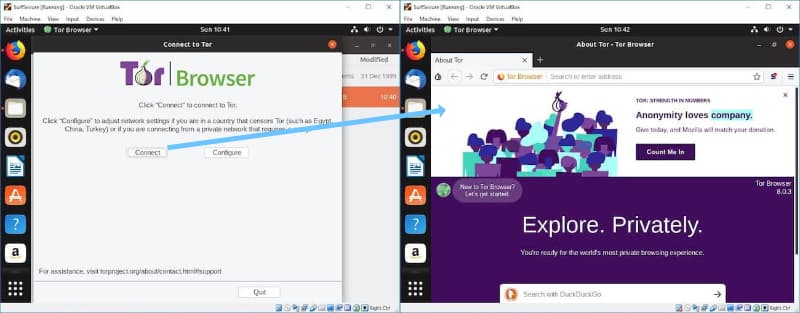
Now, the final step is to press connect and – you are in. For easier access, the next time you want to visit the dark web you can just drag the Tor Browser icon from the download folder to the desktop of your virtual machine like you would on any other computer.
Access the dark web
When I did this for the first time I was pretty disappointed. I thought it would be scarier or somehow more different. But Tor just behaves like a normal browser, you can type in the usual websites and the websites will just show up like always. So what now?
One more thing to understand when using the Dark Web is that the websites you are looking for are not linked in the usual way. Links to Dark Web sites end with .onion. The URLs of these websites look quite cryptic and the name itself does not give away much about its content. So having a repository of useful Dark Web links is essential to get your search going. By the way, Tor, the name of the browser you are using stands for The Onion Router but now let’s go and finally visit our first Dark Website.
ProPublica – A Pulitzer price winning news site, uncensored and crowdfunded. Here is the link: https://www.propub3r6espa33w.onion/
You now have all the tools up and running now. Before we actually look for study material just a quick summary of Do and Dont’s:
- Make sure your VPN is always active
- Verify your Kill Switch is enabled
- Access onion websites only with the Tor browser
- If your VM behaves infected, delete it, don’t try to repair it
- See the Dark Web as an opportunity, not a threat
- Do not download and open files from unknown or suspicious sources
- Do not contact people from illegal marketplaces
- Do not chat or reveal your identity to anyone
- Do not offer anything illegal
- If it looks suspicious it probably is
- Do not use your real email
Getting an anonymous and secure email address
Sometimes you need an email address and on the Dark
Finding study material
So the first thing we need is, of course, a search engine, something Google-like just for onion websites (or sometimes called Tor hidden services). There are several search engines you can use, here are my 3 most favorites: The first one is Ahmia (http://msydqstlz2kzerdg.onion/ )
Another popular search engine on the Dark Web is Torch which claims to have a huge repository of onion services. The link is: http://xmh57jrzrnw6insl.onion/
A third search engine you should try to find study material is “Not Evil”. This engine lets you query in title or URLs only so you can narrow down your search. Here is the URL: http://hss3uro2hsxfogfq.onion/
The next thing which is always very helpful when searching for study or any material is a Wiki. The Dark Web, of course, has one, the hidden wiki, a great source of links to more onion sites. Here is the link: http://4zkgktc6hjdmp6kw.onion/
A good resource to find books is the Z-Library. This is a huge resource for educational material, try it out here: http://2bu5puxp6afwjgql.onion/
The next one is a good site for articles and tutorials of all kinds. Check out this link to get to DeepDotWeb: http://deepdot35wvmeyd5.onion/
Note that services on the Dark Web are not always reachable so if you experience a connection timeout you might want to try another time. On DeppDotWeb you usually have a sidebar that shows you which popular sites and marketplaces are currently up.
These links should help you to get started. As you can see it is a bit more difficult to recommend educational services or dedicated websites because the focus of the Dark Web is more on other services than education. But still, it can provide additional content you can not find anywhere else.
Related Questions
Are there any educational sites on the deep web? Yes, there are search engines like Ahmia or Torch to search for study material, thinks like book libraries e.g.Z-Library or websites for tutorials and articles like DeepDotWeb. If you like to learn more about how to access start reading the whole article where I will take you into the dark web step by step.
What is the difference between the Deep Web and the Dark Web? The Dark Web is part of The Deep Web. The Deep web is the part of the Internet that is hidden because it cannot be indexed by Search engines (e.g. paid content, deliberately hidden websites, etc.). The dark web is an encrypted network (hence hidden and therefore part of the deep web) of websites accessible through means like the Tor browser and intentionally hidden from access with normal browsers.
Is it safe to browse the dark web? Absolutely. If you follow security rules like using a VPN and/or a Virtual machine, not downloading files and not deliberately trying to do something illegal the Dark Web is as safe as the “Normal” web.
How to find a list of actual dark web websites? -You can use Dark Web search engines like Ahmia or Torch or take a look at the hidden wiki to get started with a long list of onion services.
What is a Dark Web mystery box? This is not really specific to the Dark Net, it is a new hype to buy boxes of all sorts (like on eBay) with unknown content. It has been reported though that these types of boxes bought on the Dark Web contain irritating and sometimes illegal things. Don’t buy.
